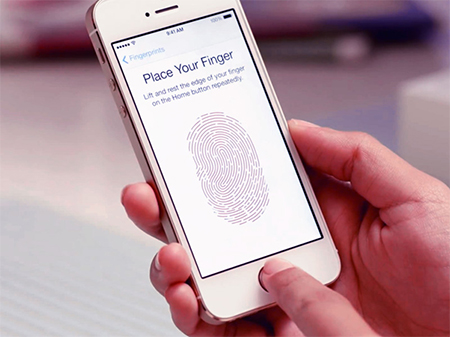
Is the Fingerprint Security Sufficient for Smartphone Security?
Image source: YouTube.com
Fingerprint scanning is a security feature common today in most smartphones. However, it may seem a personal type of security, it is still possible to breach.
Fingerprint scanners have become one of the regular features in most smartphones, whether they are the flagship or the low-end models. This additional security tool has been the result of advancements in technology, which become more accurate and faster in their readings. Scanning of the fingertips is done via four ways – optical scanners, capacitive scanners, ultrasonic scanners and cryptography plus algorithms. The capacitive scanners technology is the most common way of fingerprint scanning.
Image source: imore.com
One of the main security features of most smartphones is provided through fingerprint scanning and with a touch of a finger, the phone is unlocked and accessible. In addition, fingerprint scanning can do a lot of things like purchasing goods or services online through the smartphone and pay via Android Pay or Apple Pay. This feature can also be used to do online banking transactions such as transferring money or in paying your bills. That’s how convenient having a fingerprint scanner in your smartphone in terms of security. However, there are cases that this security feature is vulnerable. Consider the following examples:
- A recent study conducted by A. Roy, N. Memon and A. Ross (all Ph. D.s) from New York University and Michigan State University respectively entitled “MasterPrint: Exploring the Vulnerability of Partial Fingerprint-based Authentication Systems” and was published at the IEEE Transactions on Information Forensics and Security journal stated that it is possible to trick the smartphone using fake fingerprints. These fake ones can be created digitally and comes with features that are common in a human fingerprint. The study utilized various computer simulations and they tried to mimic real prints to unlock simulated phones and the result, about 65% of the time, they are able to access the simulated phones. In addition to such computer simulations, there are physical ways of breaching the security and it only takes few minutes to do it.
Image source: TechPP.com
- A biometric firm have tried accessing phones by mimicking human fingerprint. In order to do this, they showed that a dental mould is the key in making a cast and with assistance from play-dough clay that serves to fill the cast and scan the casted fingerprint to the reader – with some minor adjustment and alignment – the result was astounding as it quickly unlocked real smartphones. This primitive way is only possible if the owner of the smartphone will give green light to make a mould of his/her fingerprint.
- Technology have progressed so far and smartphone unlocking can be done, not only through computer simulation and/or the primitive method above, but through the use of 3D-scanning and printing. Is there a need for a physical fingerprint to do this? The answer is “no”, since the cast can be created from a stored image of a fingerprint. You will probably doubt this method, but this has been done in 2014 at the CCC Conference.
Falsifying a full fingerprint of a human is difficult and yet, the methods above are able to do the security breaching. The methods above take advantage of the fact that the fingerprint security only needs a portion of the fingerprint. Unfortunately, quantifying risk is difficult since Google and Apple does not divulge details about their fingerprint scanning technology.
Majority of the phone manufacturers, in fact, acknowledged that fingerprint sensors can be breached and not fool proof. However, they still make use of this technology because of the convenience it provides to numerous users. The convenience of unlocking phones outweighs the risk and hence, experts advised users to not use fingerprint scanning for sensitive apps. From the various methods mentioned above, it is true that fingerprint security can be an insufficient form of security for phone access.