More than 1 Million Google Accounts Compromised by New Android Malware
 Over a million Google accounts have been breached according to security researchers just last Wednesday. A report posted on the blog of Check Point Software Technologies, Ltd on the last day of November 2016 revealed that there’s an Android malware being used in a “new and alarming” campaign. The number of affected devices continues to rise at a rate of 13,000 per day.
Over a million Google accounts have been breached according to security researchers just last Wednesday. A report posted on the blog of Check Point Software Technologies, Ltd on the last day of November 2016 revealed that there’s an Android malware being used in a “new and alarming” campaign. The number of affected devices continues to rise at a rate of 13,000 per day.
Gooligan
This malware has been called “Gooligan” and is considered a variant of the Android malware discovered in the SnapPea app last year. What it does upon infecting devices is to collect authentication tokens that can be used to access data from user accounts on Gmail, Google docs, Google Photos, Google Play, Google Drive, and other Google services. This malware is said to specifically target devices that are running on Android 4.0 to 5.0. A vast majority of devices in current use are running these versions of Android, approximately 3 out 4 are using Android 4.0 to 5.0. For those who are not familiar with the number-based Android versions, these are Android Jelly Bean, KitKat, and Lollipop.
Check Point has already contacted Google regarding this new malware and the company says it is already working closely with the search giant to find out more about it and to reveal the source of this new malware campaign. In a statement, Google expressed appreciation over Check Point’s research and indicated that a number of steps have already been taken to protect users and improve the overall security of the Android ecosystem.
How Does the Infection Happen?
A device gets infected as an Android device user installs legitimate-looking apps from third party app stores. The malware may also be installed through a phishing campaign. It’s difficult to determine which third party apps contain the Gooligan malware code that’s why it’s advisable to avoid getting apps from sources other than the Google Play Store. Check Point actually examined some apps and found the following list of apps to be laced with Gooligan code.
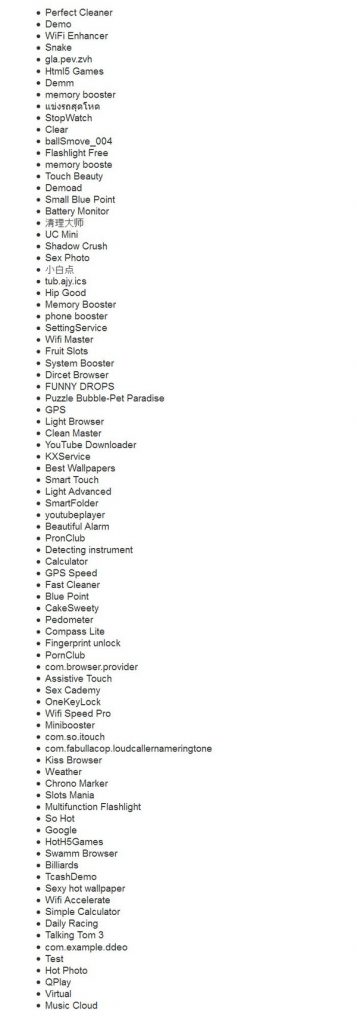
It is recommended avoiding these apps unless you get them from a reliable source. If you have any of them, be sure to have your device checked for infection.
What Does Gooligan Do?
As mentioned, Gooligan obtains data in an infected Android device. It then downloads rootkits, notably VROOT and Towelroot, and roots the infected device. After which, it downloads a new module. It also collects email accounts and authentication tokens. Additionally, it injects a code into Google Play so it can mimic the user’s actions (to avoid detection) and proceed to downloading and rating/reviewing apps depending on what the attacker instructs. Gooligan can also install adware so it can generate ad revenues.
There’s a reason why only devices running Android 4.0 to 5.0 are affected. It’s because these are the Android OS versions that have been found by Gooligan to have some vulnerabilities that can be readily exploited.
Detecting Whether or Not Your Device Is Affected
Check Point has created a convenient online tool for detecting if your Google account has been affected by Gooligan. It’s called the Gooligan Checker (click on this link to start checking your account). You will be asked to enter your email address to start the checking process.

To clarify, Gooligan infects a device so basically, if you just change your password and abandon your Android device, you are already free from it.
What to Do If Your Account Is Affected?
If your account is found to have been affected, you will have to do a reinstallation of your Android operating system and you must change your password immediately. A simple factory reset is not enough. You have to completely erase everything in your device and proceed to a clean reinstallation of the operating system with a process called “flashing” involved. Flashing requires more than just newly acquired basic skills so it is recommended asking for expert technicians to do it for you.
Where Are the Breached Accounts from?
The users affected are mostly in Asia. Around 57% of the more than 1 million accounts attacked are in Asia, 19% are in the Americas, 15% in Africa, and 9% in Europe. Since most Android users who obtain apps from app stores other than Google Play are from Asia, it’s understandable that the number of infected devices is considerably high in this part of the world.
Gooligan can be considered a major threat against Android users. Check Point actually calls the more than 1 million account breach as the largest Google account breach to date. It‘s advisable to take precautions and have your devices checked for infection as well as to have your Google account password changed. If you don’t know how to do a clean reinstallation of your Android OS, have a technician do it for you or just have your device changed. Better be safe than sorry.